SQLite Forensics Online Training
Our traditional in-class 5-day Complete SQLite Forensic Training has moved online! This new 10-day course combines both our SQLite Fundamentals class with our Advanced SQLite Forensics. Our live, instructor-led, online training provides you with the same in-depth SQLite learning experience as our on-site training over the course of 10 – 4 hour days.
Description

*Please Note: All prices listed are in USD
In this course you'll discover:
- How SQLite works at the byte‐level
- What are the different types of SQLite data components
- What are the 5 common locations to recover SQLite data
- How to perform report data validation
- How to Reverse Engineer ANY SQLite database
- Converting and identifying virtually any date format easily
- Display BLOB data within the forensic tool
- How to use a tool designed from the ground‐up as a forensic tool
- How to recover data from ‐WAL and ‐journal files
- How to reverse engineer and generate reports quickly from any SQLite database
Why SQLite Forensics?
Both Google’s Android OS and Apple’s iOS are the dominant forces in today’s cellphone market – with the market share split fairly evenly between the two companies. While these two companies are rivals, with vastly different file systems, they do share one commonality; both use SQLite as a storage container for user data. “SQLite is an in-process library that implements a self-contained, serverless, zero-configuration, transactional SQL database engine.”
Mobile Forensic Analysts can easily leverage this commonality by learning the skills required to perform low-level analysis and recovery on SQLite databases. Once learned and mastered, examiners, can then support nearly 99% of the device data they will come across in most of their mobile device examinations.
To illustrate the vast amount of work to be done, as of January 2015, the Google Play Store reported 1.43 Million Applications being available in its Google Play Store[2]. At the same time, Apple’s iTunes Store reported over 1.4 Million apps currently being available for download. That’s a total of over 2.8 MILLION apps. Even the most popular mobile forensic tool only supports parsing of 200 different applications. This support accounts for a miniscule %001 of the total apps and leaves a 99.999% gap!
Prerequisites
It is recommended students have an understanding of:
- Navigating and executing programs at the Command Line (Unix or DOS) is required.
- Beginner programming/scripting experience is helpful (but not required).
This course is reserved for active & retired Law Enforcement Only, or in certain cases examiners that have been contracted by a Law Enforcement, Military or Government Agency.
Due to the sensitive nature of our curriculum, and industry, all potential students are subject to vetting prior to enrollment. We reserve the right to refuse registration to any person that does not meet our established criteria.
Course Itinerary
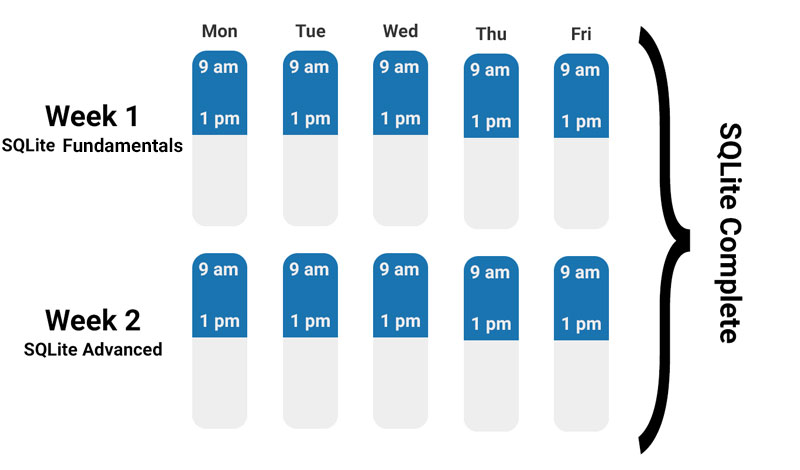
SQLite Fundamentals - Week 1
- How SQLite works at the byte-level
- What are the different types of SQLite data components?
- What are the 5 common locations to recover SQLite data?
- How to perform report data validation.
- How o Reverse Engineer ANY SQLite database.
- Converting and identifying virtually any date format easily.
- Display BLOB data within the forensic tool.
- How to use a tool designed from the ground-up as a forensic tool.
- How to recover data from .SHM, .WAL and .journal files.
- How to generate reports quickly from any SQLite database to include externally linked images.
Advanced SQLite Forensics Week 2
- SQLite Record Recovery (Incomplete and Orphaned Records)
- Manual Parsing of: Write-Ahead Logs and Journal Files
- Advanced Data Recovery Scenarios
- Manual SQLite Data Recovery
- SQLite Payload Examination/SQLite Data Construct Parsing
- Using simulations to perform data testing/verification/decryption
- SQLite Encryption
- Advance Scenario Exam
Included with Training

- A free one-year license of Sanderson Forensics SQLite Forensic Toolkit Software
- Students will receive a link to download the course material and datasets to be used in class.
Laptop Requirements
- Windows PC with two (2) USB A ports.
- Windows OS
- macOS with Bootcamp Windows
- macOS alone will not work (No Virtual Machines)
- 8GB RAM (minimum)
- 100GB storage (minimum)
- You must have admin rights or have the admin password for software installation.
- NOTE: ALL Windows updates should be done prior to class.